Cont.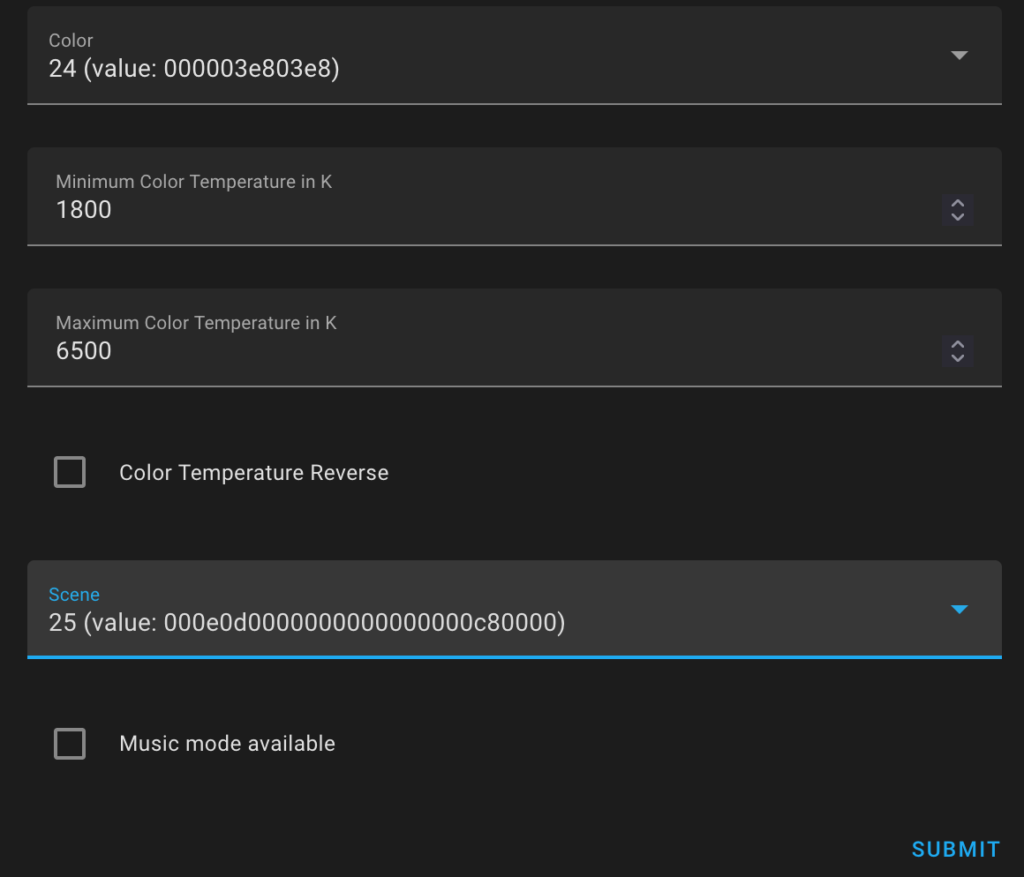 Ref: https://community.home-assistant.io/t/local-tuya-lights-issue/356659/2
Ref: https://community.home-assistant.io/t/local-tuya-lights-issue/356659/2
For “SIM Not Supported Error” when using a SIM card other than Bell/Virgin Mobile
Send you device purchase agreement to
Their process time is usually 10-60 minutes.
Customer service can’t really handle this.
Yes, there’s no lock after 2018, but the store usually lock their expensive iPhone models and unlock the carrier for you after the purchase. They do forget about the unlocking step quite often.
Why?
The scroll wheel on my MX master 3 doesn’t really work well with MacOS. Zooming is triggered by mistake quite often.
Reference: https://support.mozilla.org/bm/questions/1253302
In MacOS, meta key is the Command key. (Source)
The value 0 means “Do nothing”, 1 means “Scroll contents”, 2 means “Go back or forward in the history”, 3 means “Zoom in or out the contents”
Refer to this manual from MariaDB
https://mariadb.com/kb/en/securing-connections-for-client-and-server/
require_secure_transport = ON could be added to the my.cnf file to enforece SSL for all connections (including those from localhost & unix socket)
$pdo = new PDO('mysql:host=db.example.com;dbname=image', 'laravel', 'laravel',array(
PDO::MYSQL_ATTR_SSL_VERIFY_SERVER_CERT => false));
// under mysql => options
'options' => extension_loaded('pdo_mysql') ? [
PDO::MYSQL_ATTR_SSL_VERIFY_SERVER_CERT => false
] : []
PLEASE NOTE: array_filter in this original config file is REMOVED. Because entries with empty() value will be filtered, so that MYSQL_ATTR_SSL_VERIFY_SERVER_CERT will be removed.
MYSQL_ATTR_SSL_CA is set just to enable SSL (like mysql -h …. -u … -p –ssl)
PLEASE BE AWARE, the cert in this mode is domain validated. The MySQL server should use a cert with matched common name, ‘db.example.com’ for example. the use of domain name for the host is preferred.
Same to without verification, but set MYSQL_ATTR_SSL_VERIFY_SERVER_CERT to true. (Or just remove the attribute, since it’s true by default)
PDO::MYSQL_ATTR_SSL_CA => "/path/to/ca-cert.pem",
PDO::MYSQL_ATTR_SSL_CERT => "/path/to/client-cert.pem",
PDO::MYSQL_ATTR_SSL_KEY => "/path/to/client-key.pem",
PDO::MYSQL_ATTR_SSL_VERIFY_SERVER_CERT => false
MYSQL_ATTR_SSL_VERIFY_SERVER_CERT could be true or false, it depends.
I’m using MacOS 10.15 using PHP 7.4.11 from homebrew.
This error basically happens when PDO SSL setup/verification failed.
For example:
PDO::__construct(): SSL operation failed with code 1. OpenSSL Error messages
Or maybe
PDO::__construct(): Peer certificate CN=
Common name' did not match expected CN=domain’
I believe it’s a platform specific issue.
Mentioned already.
array_filter will filter out all attributes with value of null/false/0/”” …
Remove it when you have to use those values.
“Magnet” is damaged and can’t be opened. Delete “Magnet” and download it again from the App Store.
It could be any paid app, in my case, ‘Magnet’.
There exist a similar but common error caused by unsigned/modified third party apps (blocked by Gatekeeper)
App Is Damaged and Can’t Be Opened. You Should Move It To The Trash
This is NOT what my guide is talking about.
The error basically means Apple is unable to verify the App purchased on this machine.
The MAC address of your en0 is part of the verification. Because all Macs come with a built-in Wifi/Ethernet Adapter.
Run this in your terminal to list all network interfaces.
networksetup -listallhardwareports
What exactly happened to my is, my hackintosh motherboard comes with two built-in Ethernet adapters. I disabled one (en0) from the BIOS few days after the OSX is installed.
If you encountered the same error message, try the following:
(Software issue, basically sync your current en0 MAC address with iCloud)
(Hardware issue. in most cases, en0 not found)
Go to network settings > tiny gear icon > Set service order
Open a terminal and run:
cd /Library/Preferences/SystemConfiguration/
sudo rm NetworkInterfaces.plist
sudo rm preferences.plist
Restart machine
Credit for this: Jeremy Wininger
Official Guide: http://developer.ebay.com/devzone/rest/ebay-rest/content/oauth-gen-user-token.html
I’ll also cover some mistakes I made.
So far, we’ve done our preparation at developer.ebay.com
Then, on you local developing environment or you production server,:
On the “Your auth accepted URL“, prepare a PHP script that get the value of $_GET[‘code’] and save it in sessions. It starts with ‘v%5E1’. this is called “Authorization Code”
Next, get an “Access Token” with this “Authorization Code”
Craft a HTTP Request with whatever you like with PHP.
HTTP headers:
Content-Type = application/x-www-form-urlencoded
Authorization = Basic <B64-encoded-oauth-credentials>HTTP method: POST
URL: https://api.sandbox.ebay.com/identity/v1/oauth2/token
Request body (wrapped for readability):
grant_type=authorization_code&
code=<authorization-code-value>&
redirect_uri=<redirect_URI>
We have three ‘Variables’ here.
<B64-encoded-oauth-credentials>: Use a Chrome Browser, Right click, Inspect, Console
Then type: btoa(‘APP_ID:CERT_ID‘);
We did take down these two values earlier. and there is a : between.
Hit ENTER, the value inside the double quotes is <B64-encoded-oauth-credentials>
<authorization-code>: the ‘Authorization Code‘ we got in the callback redirect.
<redirect_URI>: This is the tricky part. This can’t be ignored or filled with random things, it’s the value of “RuName (eBay Redirect URL name)”
Send the request, and you’ll get the access token and the refresh token.
Follow the official guide to refresh the token if expired.
We are basically finished here, If you wanna call an API, ‘List orders as a seller’ for instance:
GET https://api.ebay.com/sell/fulfillment/v1/order
Headers:
Authorization: Bearer <YOUR_ACCESS_TOKEN>
It’s Bearer this time :), don’t use Basic by mistake.
VOX is the best music players on OSX I’ve ever used.
The Loop becomes one of it’s features to store unlimited music on it’s platform. It’s a good feature, and the only way for the developer to get some pay back for the wonderful applet.
I just don’t need it, and try to save some space for my menu bar.
On the VOX’s preference page, uncheck “Keep Loop Agent Running when” just doesn’t make any sense. Neither for “launchctl remove com.coppertino.VOXCloud” as the developer mentioned.
My way to close that:
Finder – Application – VOX – right click – Show package contents – Contents – Library – LoginItems
You can find the Loop.app here, but things like deleting/renaming/[removing permission] will all prevent VOX from launching.
Loop.app – Show package contents – Contents – Resources – Base.lproj
Then rename “MainMenu.nib” to something else for example: “MainMenu.nib.bye”
Quit Loop and restart VOX, Done.
It’s “OpenSSH SSH daemon configuration file”
Simply means the config file for OpenSSH Server.
Located at /etc/ssh/sshd_config
http://www.freebsd.org/cgi/man.cgi?query=sshd_config
By default, OpenSSH will listen on port 22 for all address(0.0.0.0 and ::)
There can be multiple Port defined, for example:
Port 22 Port 622
OpenSSH will listen on both ports
ListenAddress specify the address to listen, the address can be hostname, ipv4 or ipv6
You may also add an optional port number, for example:
ListenAddress 192.168.1.120 ListenAddress 1.2.3.4:922 ListenAddress ddns.example.com
OpenSSH will listen on 192.168.1.120 and ddns.example.com at port 22, plus 1.2.3.4 port 922
If there are multiple “Port” specified:
Port 22 Port 622 ListenAddress 192.168.1.120 ListenAddress 1.2.3.4:922 ListenAddress ddns.example.com
Then 192.168.1.120:22 192.168.1.120:622 1.2.3.4:922 ddns.example.com:22 ddns.example.com:622 are listened
If port is not specified, sshd will listen on the address and all prior Port options specified.
Process order: DenyUsers, AllowUsers, DenyGroups, and finally AllowGroups.
If none of the four is defined, login is allowed fro all users.
If Allow* is defined, login is only allowed to declared users and groups.
Only username and groupname are accepted, UID and GID are NOT.
In the following example, only ‘root’ and ‘user’ are allowed
PermitRootLogin yes AllowUsers root user
In the following example, only ‘user2’ is denied.
DenyUsers user2
Supposed the OpenSSH server is listening to multiple IPs (1.1.1.1 and 2.2.2.2)
At the end of sshd_config file: add:
# Only user'git' can access to server address 2.2.2.2 Match LocalAddress 2.2.2.2 AllowUsers git
You may also specify port
# Only user'git' can access to server at port 622 Match LocalPort 622 AllowUsers git
You may also specify address and port
# Only user'git' can access to server 2.2.2.2:622 Match LocalAddress 2.2.2.2 LocalPort 622 AllowUsers git
Note:
Match Introduces a conditional block. If all of the criteria on the Match line are satisfied, the keywords on the following lines override those set in the global section of the config file, until either another Match line or the end of the file. If a keyword appears in multiple Match blocks that are satisfied, only the first instance of the keyword is applied.
# Allow root only from client_ddns.example.com and Allow 'user from' 67.67.67.0/24 # Allow user2 from any host AllowUsers root@client_ddns.example.com [email protected].* user2
More details on HOST:
Host: Restricts the following declarations (up to the next Host or Match keyword) to be only for those hosts that match one of the patterns given after the keyword. If more than one pattern is provided, they should be separated by whitespace. A single
*' as a pattern can be used to provide global defaults for all hosts. The host is the hostname argument given on the command line (i.e. the name is not converted to a canonicalized host name before matching). A pattern entry may be negated by prefixing it with an exclama- tion mark (!’). If a negated entry is matched, then the Host entry is ignored, regardless of whether any other patterns on the line match. Negated matches are therefore useful to provide exceptions for wildcard matches.
At the end of sshd_config file: add:
# Only user'git' can access to server address 2.2.2.2 Match Address 67.67.67.0/24 User user AllowUsers user